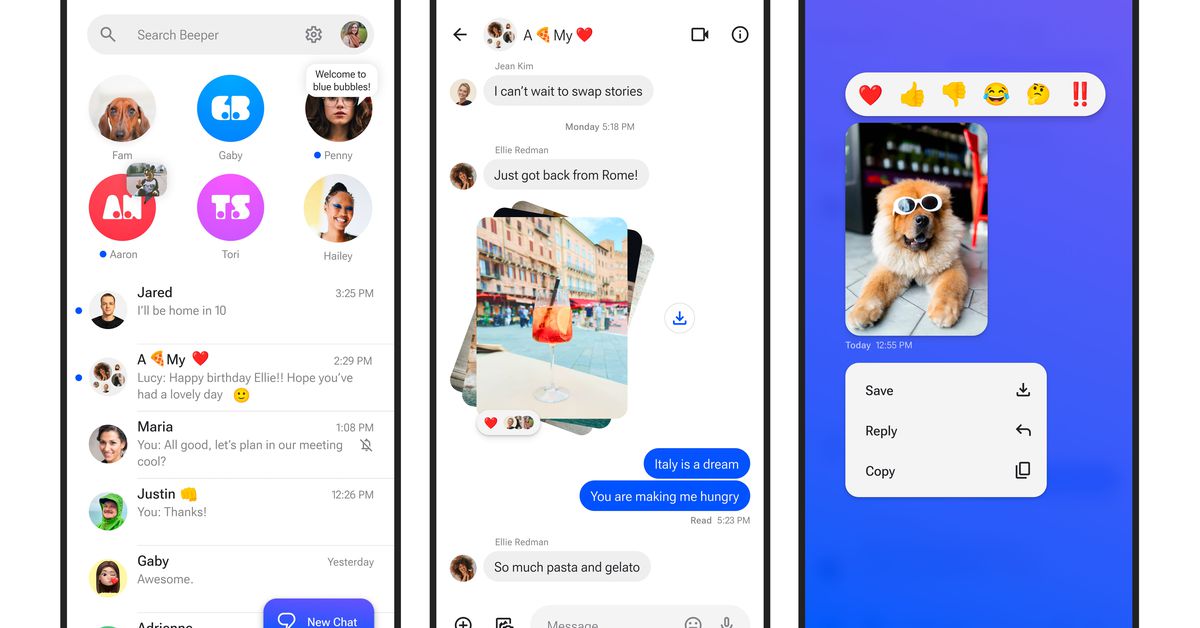
• A new Android app called Beeper Mini allows users to send iMessages as blue bubbles from non-Apple devices.
• Beeper Mini bypasses traditional iMessage hacks by directly sending iMessages from Android devices.
• The app has been praised for its smooth functionality, sending messages seamlessly between Android and iPhone users.


Sunbird worked - I was in the beta - but it turned out to have no encryption whatsoever. I am skeptical.
Sunbird just relayed messages back and forth using a Mac mini in a warehouse. They probably had something that read the messages app on there and sent to their app on the phone through their servers, and seemingly forgot to encrypt anything during this process.
This is actually sending messages as iMessage. It’s been reverse engineered which is an incredible feat, iMessage has been out like …10+ years? And no one figured it out yet until this 16yr old rocks up.
Doesn’t iMessage require some sort of Apple-issued device id? A key, unique to a device, hard-coded in the SoC? (which is easy to block if over-used).
Which is why hackintoshes used to require crazy workarounds to get this working, even with Apple’s own software, if I remember correctly (never tried myself, could be wrong).
How did they get around this? (did they?)
It does, the article actually mentions that. Yes, they did get around or reverse-engineer it. The article does not describe how, though I imagine it’s doing the same sort of workaround that Hackintoshes have to do. Honestly, it’s quite a feat.
Check out my reply
I posted some links that get into the details of how the tech works
This blog post does a fairly good job outlining the tech
You can also take a look at the pypush proof-of-concept code that this is based on
Thanks, the second link talks about this in the
"data.plist" and Mac serial numberssection.