

I’ll have a look! Cheers!
#nobridge


I’ll have a look! Cheers!


Cheers! I’ve heard of Prometheus/Grafana but VictoriaMetrics was a new one. Gonna look into it!


For signal I imagine you’ll find the best answers here:
https://github.com/signalapp/Signal-Android/blob/main/CONTRIBUTING.md
https://community.signalusers.org/c/development/android-development/22


" in" appears 25 times on the page to be exact, with 16 of those being in the table of contents and 9 being in the text afterwards.
“in” appears 54 times, as you know end up hitting “string” and so on.
Had I known that the functions table of contents was as short as it is I would probably have just scrolled.


After which ctrl+f " in" takes you to the correct chapters. I do agree that a direct link would be more helpful.
And for learning postgresql I agree it isn’t very helpful - using their tutorial links, w3schools or something like udemy if you prefer video format is the way to go in that use case.
I remember back when you were told to learn to work with the documentation, not memorize it, because you will always have access to it as a reference. Maybe bookmarking reference books/documentation will make a come back as the search engines degrade.


Your result returns version 9.0 that went EOL 2021, same as Googles fourth result in OP.
nvm, second result is correct.


I definitely feel the pain when it comes to worthless results nowadays. Though in this case DDG comes through:
Adding documentation to the search makes the “correct” page soar to the top:



I consider client devices to be a big risk factor and if I can keep them from having direct access to the Backup NAS and the IoT I consider that a big win. A simple ransomware attack on a client device would find any NFS/SMB shares the client can access and start encrypting - having the Backup NAS on a separate VLAN that only the server can access stops most of those from affecting the backup and makes restoring a lot easier. I would definitely recommend having an offline backup of the NAS as well in case of the server being breached.



I agree with this, protecting everything behind a VPN is the way to go. I help friends setup their vpn client to my stuff if I want them to access an internal service.


Computers often present their users with textual messages, but the users often don’t read them.
So many times I’ve just been a fancy TTS (Text to speech) assistant.
End user: Sends MMS of error message.
Me: Calls end user and reads the error message out loud.
End user: Oh! Thanks! Problem solved.
Me: No problem, have a good day.


If you liveboot Fedora or something with USB - how’s the upload then?
Should be a quick way to determine if it’s software or hardware based.
edit - Seems that others have had upload troubles with latest Proxmox and fixed it by downgrading:
https://old.reddit.com/r/Proxmox/comments/19d0bf7/slow_upstream_thru_proxmox81/


So… no need for a DE :)
No real need for me to remove it either, but your point stands. :)
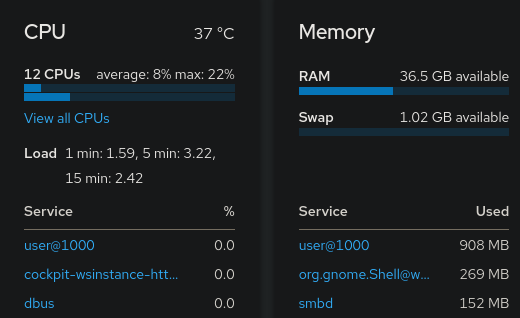


Cockpit
I do know about and use Cockpit with said virtual machine manager but I mostly use it as a shutdown/boot/restart app in my phone and a convenient service monitor and log viewer when troubleshooting.
Wireguard/OpenVPN
I really should try out Wireguard sometime but currently OpenVPN is fast enough for my bandwidth and I was already proficient with setting it up before Wireguard.
The WebUI definitely looks useful.


For linux this is as easy as script <filename>, ex:
[user@fedoragaming ~]$ script 20240313InstallingJellyfin.log
Script started, output log file is ‘20240313InstallingJellyfin.log’.
[user@fedoragaming ~]$ exit
exit
Script done.
edit: and for Windows I recommend using putty, it can also save sessions to logs.


My Debian Hypervisor do have a DE (GNOME) to be able to easily access virtual machines with virt-manager if I mess up their networking, my Debian VMs run CLI only though.
Regarding your last section I agree strongly - I only expose my vpn with no other incoming ports open. You also don’t need to invest in a domain if you do it this way.
I don’t mind helping my friends install their openvpn client and certificate and it’s nice to not have my services bombarded with failed connection attempts.


I definitely agree on starting to tinker right away and to setup snapshot/backup for your stuff and then break it. It also makes one learn how to roll back and restore which is as important as setting up the snapshot/backup in the first place.


Basic knowledge that makes selfhosting easier


Being able to selfhost game servers and allow only friends to join is sweet, I wish more games still allowed LAN connections to a selfhosted server without going through online services.


Yeah getting stuck behind CGNAT IPv4 and no IPv6 would break setting up your own vpn server. That would cause me too look for another internet provider.
I only got 100mbps at home so I’m still running openvpn as I don’t gain anything worthwhile from wireguard.
Gonna check it out!
Is it easy to setup automatic responses to the alerts, f.e. restarting a service if it isn’t answering requests in a timely manner?
Have you used it together with Windows Servers too?