Well with https enforced and secure dns not much to worry about.
Maybe from a security perspective but in terms of privacy, no. SNI can still be read, and just because DNS isn’t plaintext doesn’t mean it’s not possible to see which servers you’re talking to. And like others have said, there’s still a lot happening in plaintext at the OS and/or application level.
Still doesn’t make a VPN the “magic all in one solution” it claims to be. And SNI is encrypted on newer servers using encrypted client hello (ECH).
In terms of privacy, you’re switching around which entity gets to see a ton of details. Do you trust random public wifi enough, given modern security standards? Or do you trust a VPN company more, despite false advertising?
Use HTTPS and DoH (Becoming a default on some Android versions), and the average person will be just fine without a VPN.
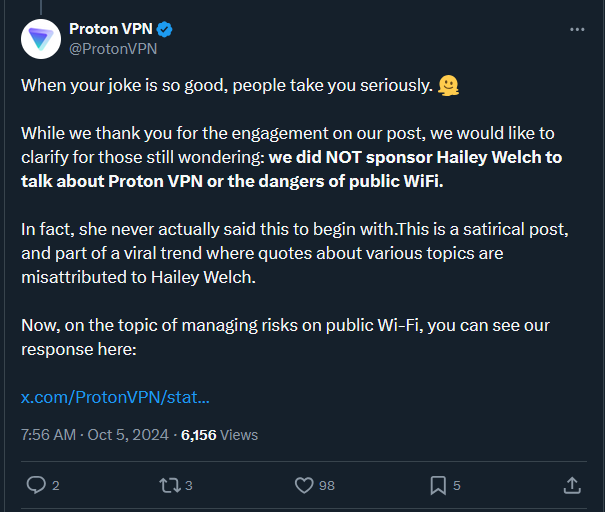
This was nothing more than a poorly executed joke from Proton. Some people are massively overreacting.
How could one have known that this was meant as a joke?
I like Proton but to me it seems like the social media person from Proton did an oopsie and as a reaction they try to save it.
"It’s a prank bro"😅 but seriously as an IT guy I’m tired of pushing VPNs down our (collective) throats, not saying the threat isn’t real but it’s really overblown by the ads
Just free, unregulated market shenanigans.
Mulvad.
I don’t understand why everyone assumes using a VPN means paying for a third party. I have Wireguard deployed in my NAS and I always have that VPN connection active on my phone to be able to access my LAN deployed services remotely, Jellyfin for example.
It’s also worth mentioning that the VPN in question, Proton, offers one of the best free tiers of any VPN company.
I don’t understand why everyone assumes using a VPN means paying for a third party.
It’s because that is what is advertised to them.
For less technical people or just don’t want to deal with public-facing open port: Tailscale or Zerotier are both great option (use Tailscale if former)!
Since Wireguard uses UDP and peers only reply to a received packet if it’s expected and valid, it won’t show up in port scans and barely increases your attack surface. Tailscale and Zerotier are quite nice, but personally I dislike NAT-punching protocols.
I tried setting this up, and I can connect to my honeserver, but I’ve no idea how to access its LAN services. How does it work?
I assumed it was a joke. My feed has been full of jokes about her talking about urban planning and transit oriented development.
The only effective antivirus program known to man is called a backup
Dude is completely right. VPNs are good against geoblocking but thats it. All VPN providers that claim not to log stuff are lying and if there are logs it doesnt make a difference privacy wise
You know, from a business standpoint, it makes financial sense NOT to log user traffic.
Reason one: plausible deniability. You can’t give what you don’t have.
Reason two: storage. Why the fuck would you keep logs, when it costs money to?
Reason three: these boots taste fantastic! (People generally don’t enjoy licking boots).
Can someone share proton’s response? I don’t have a xitter account
Nobody has a Xitter account.
https://xcancel.com/ProtonVPN you can find it here
Appreciate the alternative!
Grabbed this screenshot because I don’t trust anything on Twitter to stay visible (or the platform to even be stable)
https://protonvpn.com/blog/public-wifi-safety/#:~:text=5 ways to stay safe on public WiFi

Wow, one of a few heroes keeping Nitter alive
Fr
obviously the shitty VPNs like NordSurshark, TorGuard, Tunnelbear, cyberghost and PrivateInternetExpress suck…pretty much every VPN that’s part of some giant conglomerate sucks ass in terms of privacy and security
But then there’s iVPN, Mullvad and ProtonVPN and even Adguard VPN which do very little to no advertising at all and allow their products to speak for themselves. I mean…Kitboga and RionaPoison are sponsored by Proton, but Proton is a good company that takes their security and the security of their swiss-law-abiding users very seriously.
Don’t be a scumbag and Proton won’t snitch on you.
https://thatoneprivacysite.xyz/ is a good base for comparisons
Bear in mind that info hasn’t been updated since 2019, when the OG thatoneprivacysite sold out to a shady company. The .xyz site is an old backup someone put up of the site before it changed to only recommend a handful of bad VPNs.
Is there a more recent guide that you’d recommend?
Perhaps Privacyguides.org, but I’m not aware of a replacement for the exhausting level of detail and breadth which thatoneprivacysite once provided.
What is he talking about, public WiFi can easily poison and monitor your DNS requests (most people don’t know or use encrypted DNS), and there’s still tons of non-https traffic leaks all over the place that are plain text. Even if encrypted, there’s still deep packet inspection. VPNs can mitigate DPI techniques and shift the trust from an easily snoopable public WiFi to the VPN’s more trustworthy exit servers.
This guy really needs to elaborate on what he’s trying to say when the cyber security field very much disagrees with this stance. I’m not a huge fan of Proton, but they aren’t doing anything wrong here. You should use it for public Wi-Fi.
most people don’t know or use encrypted DNS
But a cybersecurity expert does. That’s the point. If you know those things, VPNs become obsolete, for most people. So why not teach people about it, instead of promoting VPNs?
And can you really trust an extremely profit focused company, that is built on user data, more than your local Café? If you’re in China, sure, use a VPN, they’re the lesser evil. But most spots don’t have the resources or expertise to analyze and sell or otherwise misuse your logs. VPN companies not only do, most rely on it.
If you’re a highly targeted person, it’s another story, but in that case your only hope is Tor or a new identity.
Encrypted DNS doesn’t solve everything. Handshake for TLS sessions is still in clear, you can usually see the SNI, and since we are talking about Wireless, usually this data is available to anybody who is in the vicinity, not just the network owner. This already means that you can see what sites someone is visiting, more or less. TLS 1.3 can mitigate some of this (for those who implement ESNI, but you don’t know that beforehand). Also TLS works until the user is not accepting invalid certificates prompts (HSTS doesn’t work for everything) and there are still tons of HTTP-based redirect (check mailing newsletters and see how many first send you to an HTTP site, for example) that can be used for MiTM attacks.
A VPN moves the trust to a single provider that you can choose, which is much better than trusting every single WiFi network you can attach to and the people connected to it, I would say.
Also if you pay for the VPN (I pay Proton), it’s not true that the company business is based on user data, they are based on subscriptions.
People can’t learn not to throw trash in the street, climate change that is backed by decades of science is a problem, or hell, they can’t even learn to effectively not click on super suspicious phishing links.
How on earth are they going to learn about implementing encrypted DNS when most barely know the difference between a browser and a computer.
Then they won’t know what a VPN is either.
Proton is a non profit.
But Proton Bad? I don’t understand. The armchair security nerds on Lemmy want me to hate something.
But most spots don’t have the resources or expertise to analyze and sell or otherwise misuse your logs.
Most spots don’t have also the resources or expertise to secure their own spot. As I remember, cheap routers used in public places may contain a lot of vulnerabilities.
encrypted DNS
Will it help me if I’m using LbreTorrent do download piracy content on my phone? Or how it would help me to hide my location from mobile apps that extract location from IP?
No. That’s a whole different use case. We’re discussing what most people in a public network should do. Some people, such as whistleblowers, journalists etc. maybe should use a VPN. For you grandparents, it would be pure snake oil. And even as such an endangered person, choosing the wrong, so almost all, VPNs would be even more dangerous.
For your problems, a VPN could be useful, even though for the former I would use the usenet or soap2day-like sites, which do not have you seed that content. If you still want to share it, then use a VPN. ONLY for the torrent process, not for anything else, as that would still be bad for privacy and security, as the VPN company could, and most WILL, surveil and log you. And for the latter problem, don’t use such apps except in closed environments or without internet access.
And for the latter problem, don’t use such apps except in closed environments or without internet access.
While that is a right answer, I do not want to avoid such apps because I need them. I need my mobile bank app, I need google camera, sometimes I need Google maps, etc. For me using VPN to hide my real IP from greedy apps and to hide DNS requests from the cracked public WiFi is still a good tradeoff between security, privacy and my own user experience.
If it works for you, and you found a VPN provider you can trust, or at least have the feeling of that, great! That is one of the very rare use cases where VPNs are not only useful, but actually have a purpose.
On a broader scale, most people won’t find a trustworthy VPN, and would use it for way more than they need to, essentially giving all data to the VPN company now, instead of just to the local Café or google.
And for the bank app, there is no replacement. Google’s camera can be replaced by OpenCamera, or just disallowed to access the internet, and google maps can almost perfectly be replaced by organic maps
I have Pixel with GrapheneOS and I tried most of FOSS camera apps, but all of them are still far behind the GCam. I hope one day there will be a good replacement, but not today.
I’m using Organic / OsmAnd for most of use cases and daily navigation. But if you need to find a specific office, shop, food or ATM nearby you still need GMap from time to time…
Doesn’t Graphene not support Gapps at all?
Dpi only works if they install a cert on your phone. Else they can’t crack it (in real time) or you would receive HTTPS errors
I’m not even an expert in this stuff, but with a tool I found online I demonstrated that it was easy to snoop people’s passwords on my school’s wifi networks back in the day. It took minutes.
That must’ve been quite a while ago
I mean, yes, I’m in my 40s, but it’s just as effective today.
I’m sorry, but I don’t believe it is. Nearly all traffic is TLS. When this is attacked, you’d get TLS error. Am I missing something?
There exist plenty of services on school campuses that send passwords in plaintext. There are services outside of school campuses that do, too. Hell, I’ve been able to bypass 2FA checks by just navigating around them, I don’t know what else to tell you, not everything out there uses the best security practices, so don’t assume that they do.
I guarantee you it’s not.
Yup. You can grab any unencrypted data passed between the user’s browser and a server literally out of thin air when they’re connected to an open access point. You sit happily at the Starbucks with your laptop, sniffing them WiFi packets and grabbing things off of them.
We need a switch like Firefox has that disallows anything non-HTTPS, but from the phone level. Companies like Apple and Google could also eventually warn apps that they’re going to make it the default setting.
Apps don’t use the system browser to connect to REST endpoints. Neither do they use the OS. Apps typically use a statically linked library. There are use cases for HTTP-only connections so it’s unlikely that those libraries would mess with forcing or even warning its users that they’ve used HTTP instead of HTTPS. Point is Google and Apple can do little in this regard. Unless they scan apps’ source code which could be possible to some extent but still difficult because URLs are often written in pieces.
Sure, I didn’t say they use the system browser - I said the opposite. I’m saying the OS should be able to block non-HTTPS connections. If you have control of the OS you can control what protocols are used by apps, unless I’m missing something.
What cases are there for non-HTTPS? I can’t think of any. It’s 2024. All communication should be encrypted.
The OS interfaces provided to apps (generally POSIX) have no idea what HTTP is. They’re much lower level than that. If an OS is to control what protocols are used by apps, it has to offer some functionality that does HTTP for the apps and apps have to use it. Unfortunately the only way to force that would be to disable the general OS interfaces so that apps can’t just use existing libraries that use those. If you did that your OS would become useless in other ways that rely on the basic interfaces.
The other way the OS could do anything about it is to inspect network traffic going over its network interfaces. That would be a significantly different can of worms and it’s not free in terms of processing power and therefore battery. Then you’d have the screams of privacy people that Android or iOS is looking at all network traffic.
So all in all, the OS isn’t very well suited to police application level protocols like HTTP. At least not on devices whose primary purpose isn’t network traffic related.
Just FYI https://shop.hak5.org/products/wifi-pineapple. There are ready-made devices that can do basically what you are describing!
Oh nice. Just gotta dress em up like Unifi or Aruba then stick em up on the ceiling.
Yep, my partner gave one for my birthday, it’s basically plug-and-play. It can automatically harvest credentials, spoof captive portals, etc. I bet that in most places nobody would question something like this hanging on the ceiling indeed.
How is DPI a problem if it’s encrypted? That would only work if the attacker had installed their CA cert on your client machine, right?
Yeah, deep packet inspection really doesn’t work without breaking https security via man in the middling everything.
I’m doing DPI on my own network and I can still view TLS certificate fingerprints and some metadata that provides a good educated guess as to what a traffic flow contains. It certainly better that it’s encrypted, but there is a little information that leaks in metadata. I think that’s what was meant.
I think it might be confusion between inspecting plaintext metadata like SNI vs actually inspecting encrypted contents (e.g. HTTPS content, headers, etc.).
Yeah, while it is true, lots of VPN companies are grifts just buying VPS’s and installing OpenVPN, this “Cyber security expert” puts far too much faith in HTTPS and probably never seen a lecture from the Black Hat conference
probably never seen a lecture from the Black Hat conference
Not defending Robert Graham because I’m also eyebrow raising his statement. And while you may be 100% correct that he never actually stayed to listen to a lecture, he absolutely spoke at a lot of them since 2000.
My bad for judging without checking 😔